Internet of Things (IoT)
The security of the interconnected world we live in is important to limit the exposure and vulnerability of data. Our Internet of Things research home provides us with a unique laboratory for practical research into the testing and security of IoT devices.
Research Leaders: L.Jean Camp, Xiaofeng Wang, Apu Kapadia

Usable Security
Creating usable privacy protocols combines the technical application of privacy with the understanding of human behavior to develop user-friendly security systems that will actually be utilized and provide the best possible protection.
Research Leaders: L.Jean Camp & Sameer Patil
Cryptography
With a focus on applied cryptography, SPICE development of techniques and tools to secure digital information in networks and cloud data resources.
Research Leaders: Yan Huang

Genomic & Health Data Privacy
A world leader, SPICE develops the methods and protocols for the protection or limited sharing of sensitive personal information while also addressing the ethical questions inherent in personal medical data.
Research Leaders: XiaoFeng Wang, Yan Huang, Raquel Hill


Economic Incentives and Security
Protecting sensitive information from malicious attacks requires a significant investment; designing economic incentives to compel entities to take make such an investment is a key component of risk management.
Research Leaders: L.Jean Camp

eCrime & Malware
Building systems for automated network detection of phishing, malware, and other eCrime attacks, SPICE matches system intelligence research with human studies research that builds a more scientifically driven understanding of how users perceive and use security.
Research Leaders: L.Jean Camp & Xiaojing Liao

Secure Computing
Gaining a quick understanding of the methods behind attacks is the first step toward stopping them, and preparing for future attempts is critical to securing files and systems before they are put at risk.
Research Leaders: Raquel Hill & Yan Huang

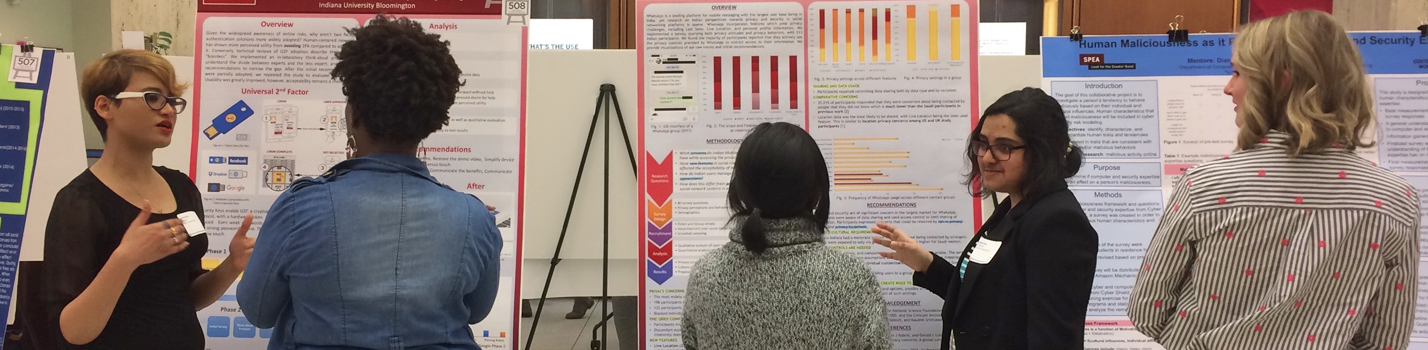
Capture the Flag (CTF)
Developing Indiana University's first Cyberdefense training class, sponsoring the Cyber Security Club, and fielding IU's first national Capture the Flag team, SPICE puts practical research and practice in the skills of both attacking and defending systems and networks in the hands of its students.
Research Leaders: Luyi Xing, Xiaofeng Wang, L.Jean Camp

Cyber Defense Educational Outreach (CTF & Hackathon)
Designing and implementing educational materials for k7-12 academic uses, public outreach, and practical threat modeling experience, our team works to build the next generation of cyber defenders with programs that include age appropriate Capture the Flag and Hackathon experiences and classroom materials.
Research Leaders: Joshua Streiff & Michele Roberts

Partnerships
SPICE partners with a variety of government, military, and industry entities making unique research and internship opportunities from CRADA agreement supported system research with CRANE to our involvement with the national Cyber Shield event at Camp Atterbury.
Research Leaders: L.Jean Camp